Cross-Device Attribution: How to Track Users Across Phone, Tablet, and Desktop
Customers don't convert on one device. Learn identity resolution techniques that connect cross-device journeys for accurate multi-touch attribution.
ONClix Team

Your customers rarely finish a purchase on the same device where they started.
We see this pattern in almost every client audit we conduct.
A potential buyer might click an Instagram ad on their phone while waiting for coffee.
That same person likely researches competitors on a work laptop during lunch.
The purchase finally happens on a tablet while they sit on the couch that evening.
Standard analytics tools usually count this as three separate people.
You see three fragmented sessions rather than one coherent story.
This fragmentation means your data is fundamentally inaccurate.
Cross-device attribution solves this by stitching these moments into a single timeline. Advanced marketing attribution software handles this identity resolution automatically, giving you a unified view of every customer.
We wrote this guide to help you understand the mechanics, the specific US privacy landscape in 2026, and how to fix your tracking.
The Multi-Device Problem
The sheer volume of devices in the US market makes tracking difficult.
We analyze connectivity reports constantly to stay ahead of this trend.
Data from Deloitte’s 2024 Connectivity and Mobile Trends survey indicates that the average US household now possesses 21 connected devices.
Your customers switch screens constantly.
They move from smartphones to desktops and back again.
Business owners and B2B buyers are even more fragmented as they juggle personal phones and corporate workstations.
We know from experience that these multi-device journeys are more valuable.
Research consistently shows that users who engage across multiple touchpoints convert at higher rates.
These users also tend to have higher average order values.
However, most default analytics setups fail to capture this value.
If you treat one person as three anonymous strangers, your business decisions suffer:
- Mobile ROI Looks Terrible: The initial phone click gets zero credit for the desktop sale.
- Customer Acquisition Costs (CAC) Are Skewed: You might turn off a winning mobile campaign because the data says it isn’t working.
- Audience Inflation: Your retargeting lists contain duplicate users.
- Wasted Ad Spend: You pay to show ads to people who have already converted on a different device.
- Conversion Rates Drop: One sale divided by three sessions equals a 33% conversion rate, whereas the reality is a 100% success for that customer.
Fragmented data leads to hesitant budgeting.
Deterministic Matching: The Gold Standard
Deterministic matching relies on hard evidence to link devices.
We consider this the “ground truth” of attribution because it uses known user data.
There is no guessing involved here.
How It Works
This method triggers when a user identifies themselves on your platform.
If a customer logs into your website on a phone and later on a laptop, we can definitively say both sessions belong to the same person.
Several identifiers facilitate this match:
- User ID: A unique code assigned when someone creates an account, which Google Analytics 4 (GA4) uses as its primary key.
- Email Address: The most common connector, often captured during checkout or newsletter signups.
- Phone Number: Useful for SMS marketing and connecting mobile usage.
- CRM IDs: Critical for B2B, linking Salesforce or HubSpot contacts to site activity.
Strengths and Limitations
Accuracy is the primary benefit of deterministic matching.
We rarely see false positives with this method.
If the login credentials match, the user is the same.
However, scale is a major hurdle.
You can only track users who actively log in or identify themselves.
Most website traffic remains anonymous.
We typically see that only 10% to 30% of site sessions involve an authenticated user.
This leaves the vast majority of your traffic in the dark.
Relying solely on logins creates a “logged-in bias” in your data.
Probabilistic Matching: Filling the Gaps
Probabilistic matching uses algorithms to make educated guesses about anonymous users.
We use this to track the 70% to 90% of users who never log in.
It analyzes thousands of signals to calculate the likelihood that two devices are related.
Signals Used for Probabilistic Matching
- IP Address: Devices connecting from the same residential WiFi often belong to the same household.
- Geographic Patterns: GPS data showing two devices at the same coffee shop every morning suggests a link.
- Device Fingerprinting: A combination of screen resolution, OS version, and browser fonts creates a unique profile.
- Temporal Proximity: A phone goes idle and a laptop becomes active immediately after at the same location.
Strengths and Limitations
This method expands your view significantly.
We often see coverage rates jump to 60% or 80% when probabilistic modeling is applied.
It allows you to attribute value to top-of-funnel blog readers who haven’t subscribed yet.
The downside is a lack of absolute certainty.
Probabilistic matches are predictions, not facts.
A confidence score accompanies every match.
Scores above 90% are generally actionable for business decisions.
Lower scores can introduce noise and errors into your reporting.
We recommend a hybrid approach for the best results.
Use deterministic data where available, and fill in the blanks with probabilistic modeling.
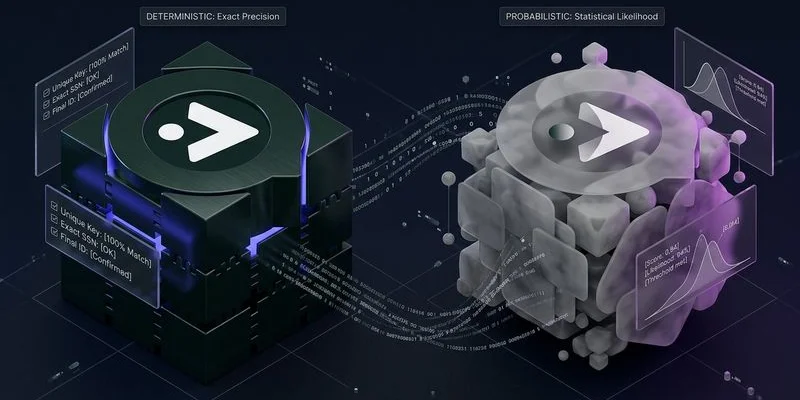
Comparison: Deterministic vs. Probabilistic
Business owners need to understand the trade-offs before investing in tools.
We use this breakdown to simplify the decision:
| Feature | Deterministic Matching | Probabilistic Matching |
|---|---|---|
| Accuracy | Very High (99%+) | Variable (60-90%) |
| Reach | Low (Requires Login) | High (Includes Anonymous) |
| Primary Data | First-party (Logins, CRMs) | Signals (IP, Device ID) |
| Cost | Low (Internal data) | Medium/High (Third-party tools) |
| Best Use | Retention & LTV Analysis | Acquisition & Top-of-Funnel |
Identity Graphs: The Foundation of Cross-Device Attribution
An identity graph is the database that powers this entire process.
We view it as a map of your customers and their devices.
It acts as a central repository where cookies, emails, and device IDs are stored and linked.
How Identity Graphs Work
Imagine a customer named Sarah.
Sarah visits your site on her iPhone and gets a generic cookie ID.
Later, she visits on her iPad and gets a different cookie ID.
Eventually, she clicks a link in your email newsletter on her iPad.
The identity graph now links the iPad cookie to her email address.
Because her email is also linked to her past iPhone purchases, the graph connects all three points.
The system now understands that the iPhone visit and the iPad visit are the same person.
A robust graph unifies various identifiers:
- Cookies (even if they expire).
- Mobile Ad IDs (MAIDs).
- Hashed Email Addresses (HEMs).
- Physical Addresses.
- Connected TV IDs.
Building vs Buying an Identity Graph
You have two main options for accessing an identity graph.
We generally advise against building one from scratch unless you are a massive enterprise.
The engineering overhead is immense.
You must manage server infrastructure, complex matching algorithms, and constant data cleaning.
Privacy compliance with US state laws like CPRA makes self-management even riskier.
Most business owners achieve better results by “renting” this capability.
Platforms like Segment, Tealium, or specific attribution tools handle the graph for you.
We also see success with platforms like LiveRamp or The Trade Desk (Unified ID 2.0).
These services maintain the connections so you can focus on strategy.
Platforms like ONClix integrate these graphs directly into their tracking.
This removes the technical burden of identity resolution from your team.
Implementation Tips
Effective attribution requires more than just buying a tool.
We have compiled a list of practical steps to improve your data quality immediately.
Maximize Authentication Touchpoints
You need to give users a reason to log in early.
We suggest moving away from “guest checkout” as the default.
Offer tangible incentives for identification.
A 10% discount code for email signup is a classic tactic because it works.
Loyalty programs or “save for later” wishlists are also excellent for capturing IDs across devices.
Implement Consistent First-Party Tracking
Browser restrictions are reducing the lifespan of standard cookies.
We see Safari’s Intelligent Tracking Prevention (ITP) deleting client-side cookies in as little as 24 hours.
You must implement server-side cookie setting.
This involves using a custom domain (like tracking.yourdomain.com) to set cookies.
First-party server cookies can persist for months rather than days.
Longer cookie life gives you a better chance of spotting the user when they return on a different device.
Counteract Link Tracking Protection
New updates in iOS 17 and macOS Sonoma explicitly strip tracking parameters from URLs in Mail and Messages.
We have observed that parameters like gclid (Google) and fbclid (Facebook) are often removed before the user lands on your site.
You must adapt by using clear, distinct UTM parameters that do not rely on these click IDs.
Review your URL structure to ensure critical campaign data is passed through standard UTMs rather than proprietary click identifiers.
Use Server-Side Event Collection
Ad blockers and browser privacy settings prevent many tracking scripts from loading.
We strongly advise utilizing Server-Side Google Tag Manager (sGTM).
This moves the tracking burden from the user’s phone to your server.
It ensures that data is captured even if the user has strict privacy settings.
Cleaner data inputs lead to better matching in your identity graph.
Hash Personal Identifiers
Security must be your priority when handling customer data.
We use SHA-256 hashing to secure emails and phone numbers before they ever leave your server.
This turns “[email protected]” into a unique string of characters.
The identity graph can match the string without ever seeing the actual email.
This is critical for complying with US privacy regulations like the California Consumer Privacy Act (CCPA) and the Virginia Consumer Data Protection Act (VCDPA).
Set Realistic Expectations
No system will track 100% of your users.
We remind clients that the goal is “directional accuracy,” not perfection.
Some users will always remain anonymous.
Some devices will never be linked.
If you can connect enough journeys to see the real value of your mobile ads, you have won.
Do not let the pursuit of perfect data paralyze your decision-making.
The Impact on Attribution Accuracy
Correcting your attribution model changes how you view your business.
We frequently see attributed conversions for “upper funnel” channels increase by 15% to 30%.
Campaigns that looked like failures often reveal themselves as essential first steps.
Conversely, “direct traffic” conversions usually decrease.
You stop giving credit to the last device and start crediting the marketing that actually created the demand. A multi-touch attribution model combined with cross-device tracking gives you the most accurate picture possible.
This clarity allows you to allocate your budget with confidence.
Business owners can finally see the true ROI of their social media and display ads.
We know that seeing the full picture is the only way to scale efficiently in 2026.
